If you want to secure data on Windows 10 inside your PC, there are certain features. These features known as Encrypting File System and BitLocker drive encryption. Microsoft has introduced to have secure data inside your computer from other standard users account and unauthorized parties. The file encryption process inside your Windows can make your files inaccessible for other standard user accounts or Unauthenticated access procession inside your computer. It is a way of protecting data form attackers, spies, and online criminals. Only some with the correct password or authorized by administrator cloud access those files and directories.
Keeping windows files safe is a very big deal these days. Even encrypted files are not 100 percent secure. If you think that there is someone snooping at you or your data is getting a password attack from some unauthenticated users. You can put a password on your file and have secure data even it was stolen.
In this article, we have revealed encryption tools on Microsoft Windows (EFS and BitLocker) and how to encrypt files on windows 10 without using any extra devices or third-party software.
Differences between EFS and BitLocker
Encrypting File System (EFS) and BitLocker are a build-in features introduced for the file encryption on Microsoft operating systems. EFS allows you the individual file encryption in the meantime BitLocker encrypts the entire volume of your hard drive inside your Windows OS.
BitLocker is the most secure file restriction option for your windows files. Third-party software is the second most secure restricted container for your files. Encrypting File Services or (EFS) is the third option for the file encryption inside your windows 10.
This is because of fewer security services and decryption options that EFS has. Anyone who could have physical interaction with the PC or your hard drive can easily break your password and use the administrator authentication to open the files, as this option is based on NTFS files the invader can easily take your files to a pen drive with the NTFS format.
BitLocker
BitLocker encryption technology encrypts the entire volume of your Disk drives. To open the file protected with BitLocker, no-matters whom you are logging in, you should have the correct password even the administrator account users. Do not forget to always have a password backup of your files restricted with BitLocker, or unencrypted copy of your files anywhere secure.
If you forget your BitLocker password, there would be no resetting option, until you would have your files password backup recovery. BitLocker uses the TPM chip which stands for (Trusted Platform Module). It is a microchip functioned to support enhance security features.
To check the TPM chip availability inside your computer:
- Method 1: Hold the windows + R to open the run dialog box and type tpm.msc. If the trusted platform module is opened, it means your system has the TPM chip. If there was some kind of message then it means your pc doesn’t have the TPM chip.
- Method 2: Go to the Search bar, search for Control Panel> Hardware and Sound> Device Manager from Device manager expand the Security devices. If your device has a TPM chip inside, you will get your TPM chip with its module number written on there.
- Method Number 3: press the Windows key + X on your keyboard, click on Device Manager> Security devices or simply go to the Search bar, search for Device Manager from Device Manager expand the security devices and go so on.
- Learn about Microsoft’s New Privacy Protection Tools- Edge Chromium
- How To Reset Forgotten Windows 10 Password?
How to encrypt drives using BitLocker on Windows 10?
To run the BitLocker drive encryption on your HardDisk, the TPM security platform chip is acquired. The TPM chip supports the enhanced security features which is awesome. There is some security configuration you need to have on your drive before you run the BitLocker drive encryption process.
BitLocker can be set up in two ways:
1: Allow BitLocker with a Compatible TPM
Microsoft built better software using secure design, secure code, and security testing. Trusted Platform Module (TPM) is a standard security platform microchip to protect your password and disk encryption inside your device.
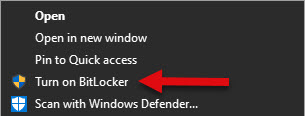
To run BitLocker with a compatible TPM chip you do not need any configuration. Go to the This PC Right-click on the drive you want to encrypt and click on Turn on BitLocker. After you turn on BitLocker your computer will perform the same steps as you encrypt your drive without a compatible TPM chip. In this option, you just can make your own password rather than 0-9 PIN numbers. So, we will focus on the second method.
2: Allow BitLocker without a compatible TPM chip.
This feature enables you the additional authentication requirement at your startup. with this feature, you can enter a number key or insert a USB pen drive as a trigger to open the media hard drive inside your computer. To run this feature:
- Press the Windows key + R on your keyboard and type gpedite.msc. The Local Group Policy Editor screen will come out, from there expand the Administrative Templates.
- From Administrative Templates expand Windows Components.
- Expand BitLocker Drive Encryption.
- Expand Operating System Drives.
- Double-click on Require additional authentication at startup.

- Click on Enable, and do not forget to have checked the Allow BitLocker without a compatible TPM chip then click on Apply. Click Ok and you are done.
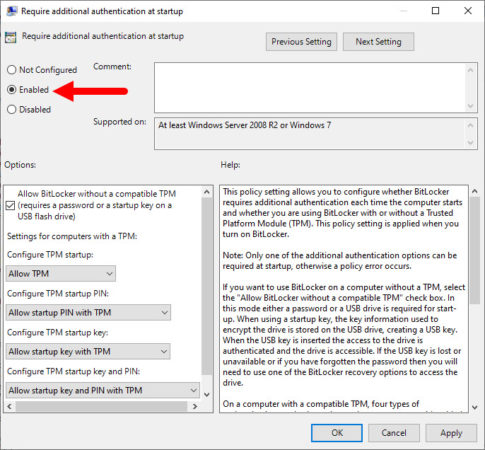
What is Require additional authentication at startup Policy? For more go to the end of this post and increase your information.
After you configured your Local Computer Policy this feature helps you keep your data more secure, you can have BitLocker prompt you to enter a PIN or insert a USB flash drive each time you boot up your PC. Follow the following steps to have successful drive encryption :
Step 1: Turn on BitLocker
Right-click on the drive and click on turn on BitLocker. When you turn on BitLocker after checking some system requirements your computer will perform these following steps.
Step 2: Select or choose how to unlock your drive at startup.
If you want your files more secure, BitLocker prompt you to enter a PIN (Number key) or insert a USB media drive each time you start your PC.
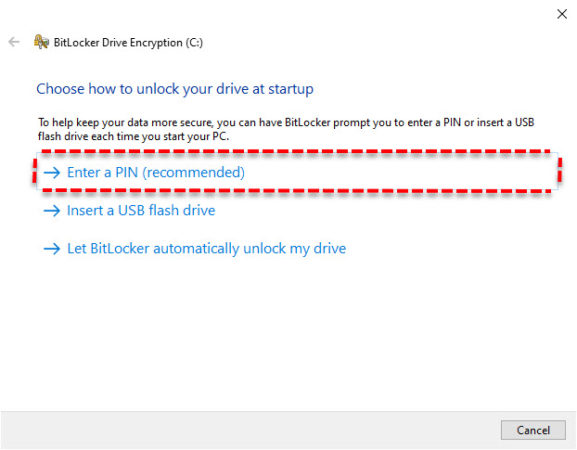
Select Enter a PIN which is recommended.
Step 3: Enter your PIN twice (remember the PIN code is 6-20 numbers long, no-letters as always).
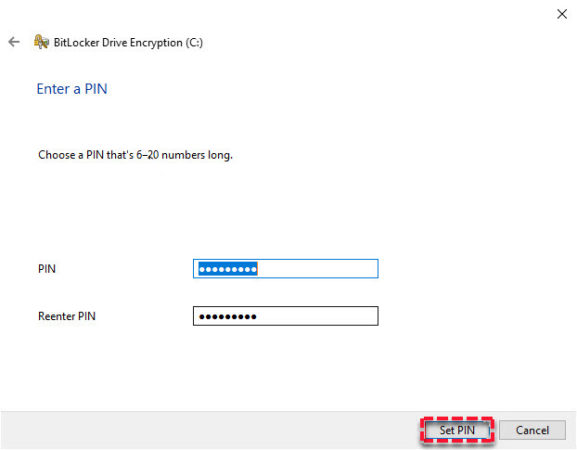
After you entered your number key click set PIN to continue.
Step 4: How you want to back up your recovery key? A recovery key can be used to access your files and folders if you’re having problems unlocking your pc. You get three options for this, save your recovery key to your Microsoft account, save to a file inside your computer or print the hard of your recovery key. It is good to have more than one and keep each in a safe place other than your PC.
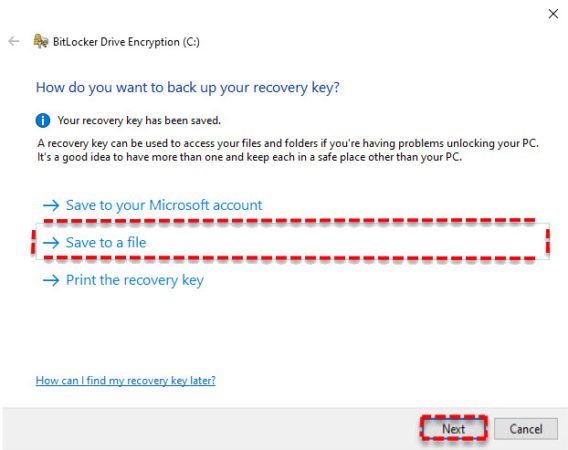
After you saved your recovery key, click Next to continue.
Step 5: Choose how much of your drive to encrypt.
if you’re running up BitLocker on a new PC, Encrypt used disk space only is faster and best for new PCs and drives. BitLocker encrypts automatically new data as you add it.
if you’re enabling BitLocker on a PC or drive that’s already in use, Encrypt entire drive is slower and can take a while but the best option for PCs and drives already in use. Encrypting the entire drive ensures that all data is protected-even data that you deleted.
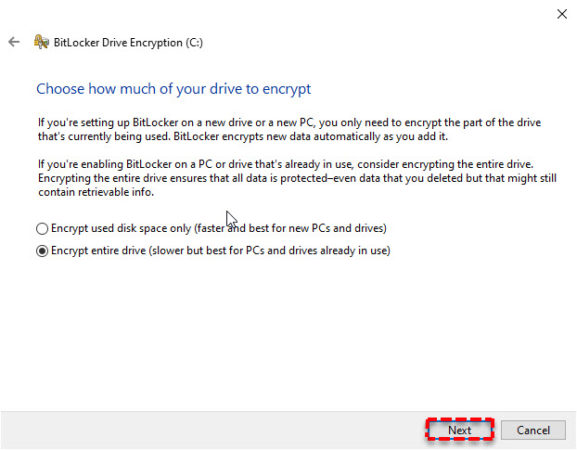
We will select the second one and click Next to continue.
Step 6: Choose which encryption mode to use.
If you are encrypting a fixed drive inside your computer, the New encryption mode is best and compatible with Windows 10 version 1511 and later.
if that’s a removable drive such as USB flash drives and external hard drives, Compatible mode is best for drives that can be moved from your device.
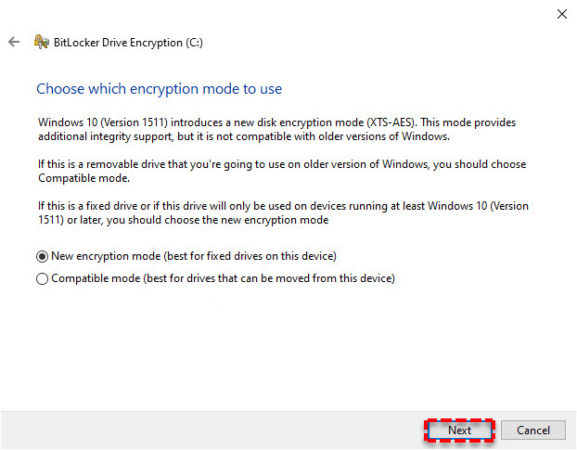
Select the first one and click Next to continue.
Step 7: Are you ready to encrypt this drive?
BitLocker Drive Encryption encrypts the entire volume of your hard drive and which can take a while when you start the encryption process but you can keep working while the drive is being encrypted.
checking the “Run BitLocker system check” ensures that BitLocker can read recovery and encryption keys correctly before encrypting the drive.
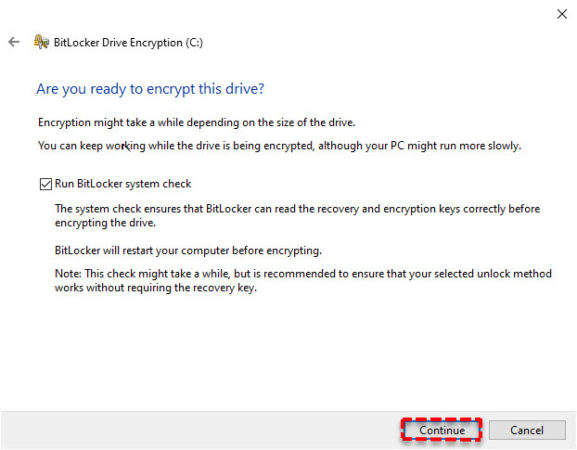
check the Run BitLocker system check and click on continue.
step 8: Rebooting the device.
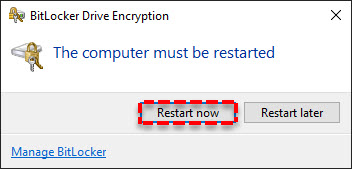
The removable drive encryption doesn’t need restarting your PC. but for internal drives, it is a must to restart the computer.
Third-party software’s
After BitLocker Third-party software is the most secure file-encrypting containers for your windows files. If you wished to have a password-protected container inside your computer. This encryption software’s tool allows you to have your all private files save inside a password-protected container.
If you are running a Windows OS home addition. BitLocker and EFS encryption file services are not enabled for home addition windows. So, how I am going to have encrypted files on windows 10 home? Or is there any third option for my file’s security? Yes, there is always a third option. Third-party software’s are more secure than the EFS and you can also get them for free. Or simply you can upgrade your windows home addition to any enterprise or pro addition.
Free apps to encrypt files in home addition windows:
- VeraCrypt
- 7-zip
- GNU Privacy Guard
- AxCrypt
Encrypting File System (EFS)
Encrypting File Services (EFS) is a Microsoft windows build-in feature to encrypt the individual files. This feature is introduced on Microsoft windows for encryption of NTFS format drives and directories.
Encrypting File System is an easy and quick way to protect your files individually but isn’t as secure as other methods, like BitLocker. because if you are not going to have your entire drive encrypted, EFS enables you manually encrypt separate files and folders. other standard user accounts can open the folder but cannot access the files without having the access authentication or decryption key.
How do I encrypt files on windows 10 using EFS?
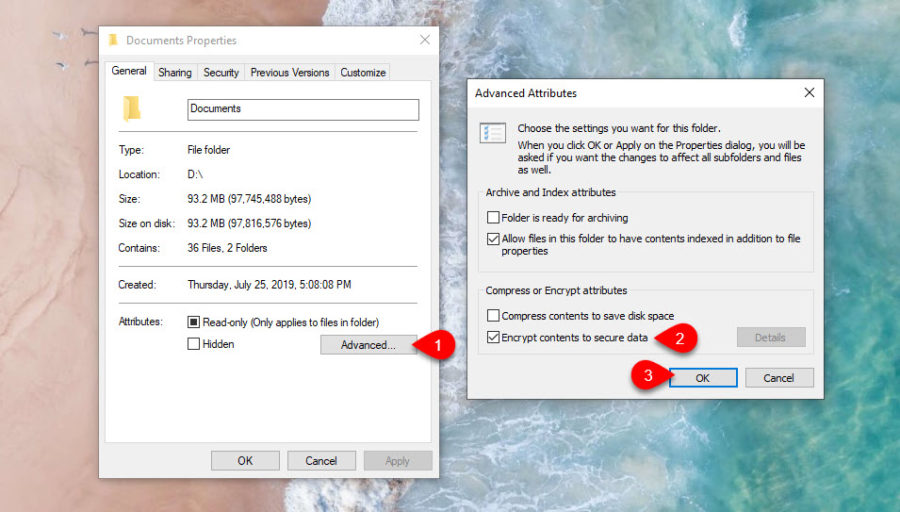
Step1: Right-Click on the file and go to the Properties> Advanced.
From advanced attributes select Encrypt contents to secure data then click Ok, click Apply.
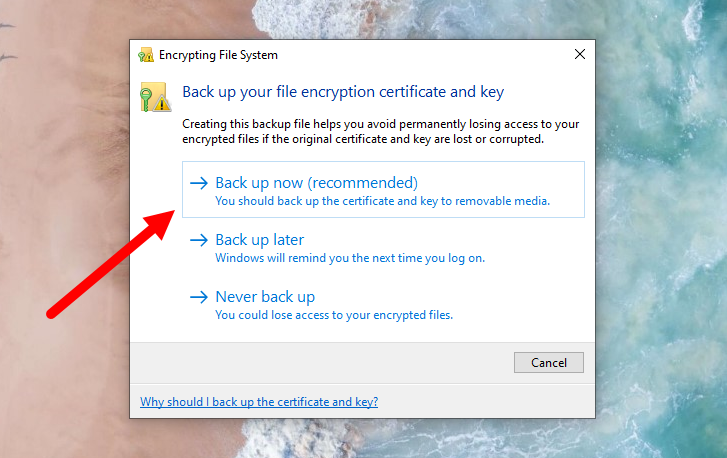
Step 2: Back up your file encryption key
You will get a key backup notification of your encrypted files near the action center. This will help you avoid permanently losing access to your encrypted files if the original certificate and key are lost or corrupted?
click on Back up the file and from backup options click on backup now (recommended).
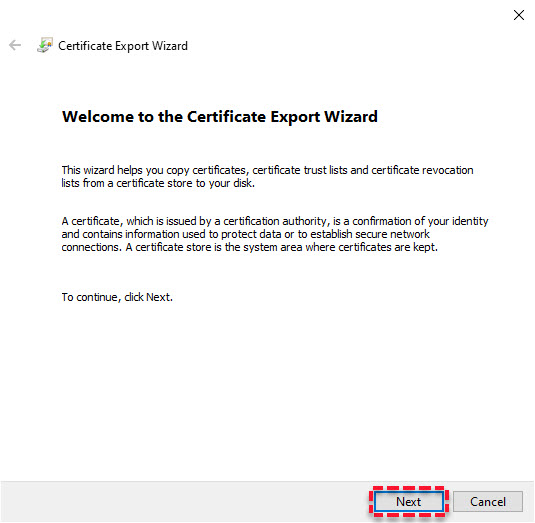
Step 3: Copy your encrypted files certificate and key. This process will backup the certificate and key to a removable disk. From certificate export wizard click Next to make a certificate for your file.
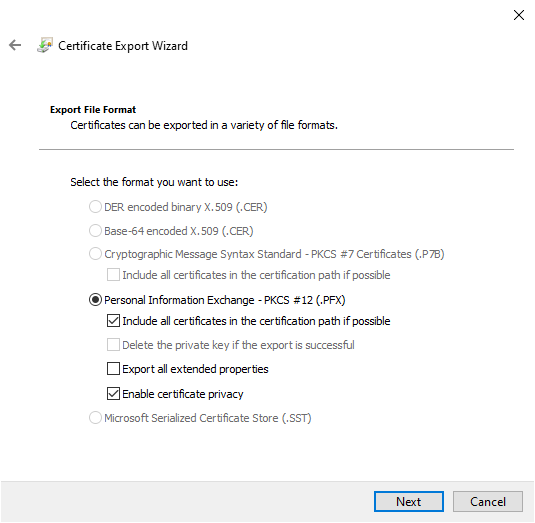
Step 4: file formats.
you can save your certofocate Your encrypted file certificate would be safe with the .pfx file format. click Next to continue.
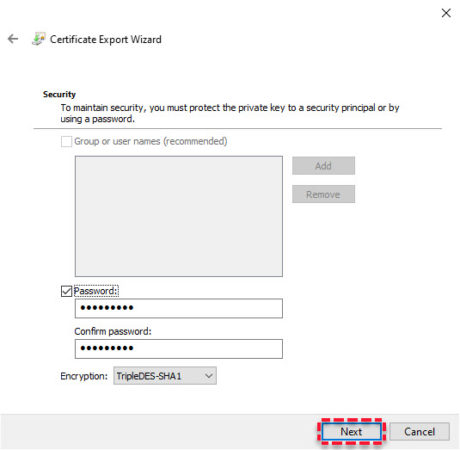
Step 5: check your password box; enter your password twice. Click Next to continue.
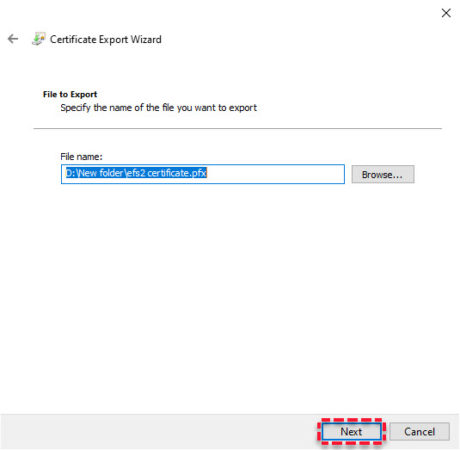
Step 6: choose the place you want to save the certificate then put a name on your certificate and click save. (Remember guys because it is an export certificate. for some security reasons, it is good to export the certificate into a USB drive rather than the windows drives. after your work is done, take your pin drive to any save place you want.)
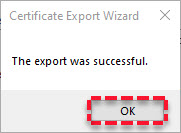
Step 7: Click Next> Finish and your certificate would be exported successfully.
Notice: the file certificate backup screen appears once for the first time after that we won’t get that notification. So, it is necessary to have your file certificate backup.
How to decrypt the EFS encryption?
For the decryption of your files right-click on the file go to the Properties> Advanced from the Advanced attribute uncheck the Encrypt contents to secure the data, click Ok then click on Apply, click Ok, and you are done.
What is Require additional authentication at startup Policy?
This policy setting allows you to configure whether BitLocker requires additional authentication each time the computer starts and whether you are using BitLocker with or without a Trusted Platform Module (TPM). This policy setting is applied when you turn on BitLocker.
Note: Only one of the additional authentication options can be required at startup, otherwise a policy error occurs.
If you want to use BitLocker on a computer without a TPM, select the “Allow BitLocker without a compatible TPM” check box. In this mode either a password or a USB drive is required for start-up. When using a startup key, the key information used to encrypt the drive is stored on the USB drive, creating a USB key. When the USB key is inserted the access to the drive is authenticated and the drive is accessible. If the USB key is lost or unavailable or if you have forgotten the password then you will need to use one of the BitLocker recovery options to access the drive.
On a computer with a compatible TPM, four types of authentication methods can be used at startup to provide added protection for encrypted data. When the computer starts, it can use only the TPM for authentication, or it can also require insertion of a USB flash drive containing a startup key, the entry of a 6-digit to 20-digit personal identification number (PIN), or both.
If you enable this policy setting, users can configure advanced startup options in the BitLocker setup wizard.
If you disable or do not configure this policy setting, users can configure only basic options on computers with a TPM.
Note: If you want to require the use of a startup PIN and a USB flash drive, you must configure BitLocker settings using the command-line tool manage-bde instead of the BitLocker Drive Encryption setup wizard.

1 thought on “How to encrypt files on windows 10?”
Comments are closed.